Case studies of some of the famous malware.
As part of the malware analysis series from the part – 1 we learned what are the different types of malware and how do they target and affect the system, now lets dive deeper into some of the infamous malware case studies through which we will understand how much damage a malware cost to the economy, scientific research, and in peoples life. through this case study we will learn how sophisticated are these malwares using various strategies to enter the victim system and how these malware more than one zero day exploits. i have gathered the case study of different types of malware to get a better understanding of the impact of malware in various vectors
MIRAI DYN Botnet
Mirai, which translates to ‘future’ in Japanese, is a notorious botnet known for its ability to carry out complex, multi-vector attacks, making mitigation incredibly challenging.
The 2016 Mirai attacks were especially significant not only for the scale of the damage but also for the release of the botnet’s source code. This allowed individuals with even basic IT knowledge to create their own botnet and launch Distributed Denial of Service (DDoS) attacks with minimal effort.
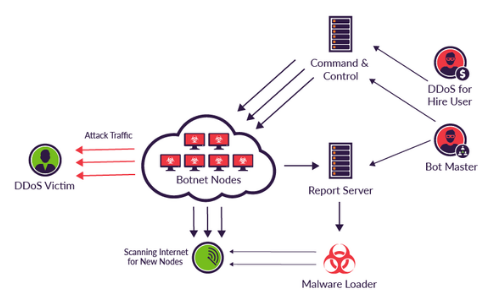
At its core, Mirai works by scanning the internet for vulnerable IoT devices, specifically targeting those with open ports or default usernames and passwords. Once it identifies a weak target, it exploits these vulnerabilities to gain access and infect the device with malicious code.
As a result, the compromised device becomes part of the Mirai botnet, which can then be controlled remotely through a central “command & control” (C&C) server. The C&C server enables attackers to coordinate large-scale DDoS attacks against websites, networks, and other digital infrastructure, harnessing the collective power of all the infected devices. Mirai is particularly effective against devices running on ARC processors, which typically use a simplified version of the Linux operating system. When these devices are left with default login credentials, Mirai can easily gain control and add them to its botnet. This combination of widespread vulnerabilities and easy access makes Mirai a powerful and dangerous tool for cybercriminals.
Wanna Cry
The WannaCry ransomware attack in May 2017 wreaked havoc across over 350,000 devices within just four days. Though the attackers received only a modest payout of $100,000, the estimated losses in productivity and data destruction soared into the billions.
What made WannaCry particularly dangerous was its ability to spread as a worm, unlike traditional ransomware that relies on infected links or websites. This allowed infected devices to propagate the attack to other systems.
WannaCry exploited the EternalBlue vulnerability, discovered by the NSA in older versions of Windows. By targeting the Windows SMB protocol, the ransomware was able to remotely execute malicious code through specially crafted packets. The attack began with a dropper packet, followed by an unusual step—connecting to an unregistered domain. If this connection failed, the malware would continue its attack by sending two more packets to encrypt files and display a ransom note. Victims were demanded to pay $300 in Bitcoin, with escalating deadlines and the threat of file deletion if the ransom wasn’t paid. Using both RSA and AES encryption, WannaCry made manual decryption extremely difficult within the time limits.
Ironically, a “demo” feature would decrypt ten files at random, potentially convincing victims to pay, though the bad coding of the ransomware meant there was no guarantee they would recover their data.
Zeus Trojan
The Zeus Trojan, also known as Zbot, is a notorious and highly effective malware attack that has been causing widespread issues since its creation in 2007.
Initially used to target the U.S. Department of Transportation, it gained significant attention when its code became publicly available in 2011, leading to numerous variants. Its fileless nature makes it particularly challenging for antivirus software to detect, further enhancing its effectiveness.
Zeus primarily spreads through two methods: drive-by downloads and phishing attacks. Drive-by downloads occur when users unknowingly visit websites containing malicious code that automatically installs malware. While modern browsers like Google Chrome often block these, older browsers such as Internet Explorer remain vulnerable. The second method, phishing, involves tricking users into downloading harmful software via deceptive emails or social media links. The main objectives of Zeus are to steal sensitive financial information and add infected machines to a botnet.
Unlike other malware, most Zeus variants avoid causing lasting harm to infected devices, instead focusing on evading detection to collect valuable data over time. By 2014, it was estimated that up to one million computers worldwide were infected with the Game over variant, making it one of the most extensive botnets in history.
Stuxnet
Stuxnet, discovered in 2010, was a highly sophisticated computer worm designed to target industrial control systems (ICS), particularly those used in critical infrastructure such as power plants and water treatment facilities.
The worm’s most notable target was Iran’s nuclear enrichment facilities, where it caused significant disruption. Stuxnet specifically attacked Siemens Step7 software, used in SCADA systems, and focused on manipulating the centrifuges used for uranium enrichment. It spread via infected USB drives, exploiting vulnerabilities in “air-gapped” systems—those not connected to the internet. The malware utilized four zero-day exploits, flaws previously unknown to software vendors, to remain undetected. The worm’s functionality was twofold: surveillance and sabotage.
It secretly monitored the targeted systems, altering the centrifuge speeds to cause physical damage while feeding false data to operators to avoid suspicion. The malware was highly specific, activating only under certain conditions to minimize collateral damage outside its intended targets. Stuxnet also employed rootkit capabilities to conceal its presence and modified Programmable Logic Controllers (PLCs) to alter equipment behavior.
The attack caused significant damage to Iran’s nuclear program, destroying nearly 1,000 centrifuges at the Natanz facility and revealing critical vulnerabilities in ICS systems globally. Though it remains officially unacknowledged, it is widely believed that Stuxnet was a joint operation between the United States and Israel, as part of a covert mission known as “Operation Olympic Games.”